As Cybersecurity Month kicks off this October, it’s more important than ever to recognise the vital role that cyber awareness plays in our daily lives. From the rise in sophisticated cyber threats to the increase in remote working, the digital landscape is more vulnerable than ever.
At SOS Intelligence, we believe that cybersecurity is not just the responsibility of IT professionals or tech giants; it’s an essential concern for every individual, business, and organisation.
The Ever-Evolving Cyber Threat Landscape
The world of cyber threats is in constant flux. As technology advances, so do the methods employed by cybercriminals. These threats are no longer limited to large corporations or government bodies; anyone with an online presence is at risk. With more and more of our personal and professional lives being conducted digitally, the risk of cyberattacks is ever-present. But what are the current threats we should be aware of, and why is cybersecurity awareness critical for everyone?
1. Phishing and its Evolving Variants: Smishing, Vishing, and Quishing
Phishing remains one of the most prevalent and dangerous forms of cyberattack. At its core, phishing is a social engineering attack where cybercriminals impersonate legitimate organisations or individuals to deceive victims into divulging sensitive information, such as passwords, financial data, or personal identification. These attacks typically arrive as emails, with significant work by threat actors to make them look authentic, often by mimicking well-known brands or institutions.
But phishing has evolved significantly in recent years, and new variants like smishing, vishing, and quishing have emerged. Each of these methods follows the same principle of deception but uses different communication channels to target victims.
Traditional Phishing
Traditional phishing attacks most commonly occur via email, where attackers craft messages that appear to come from trusted sources. These emails often contain malicious links or attachments designed to steal login credentials, infect systems with malware, or gain access to private accounts. Common phishing examples include emails purporting to be from banks, online shopping platforms, or cloud service providers, asking the recipient to “verify” their account details or “reset” their passwords.
Why Awareness Matters: Despite phishing being a widely known tactic, many people still fall victim to it. Email is an essential tool in both professional and personal life, which is why it remains a primary target for attackers. Recognising the signs of phishing emails—such as spelling mistakes, suspicious email addresses, or urgent requests—can help individuals avoid being tricked into revealing sensitive information.
Smishing (SMS Phishing)
Smishing is the SMS (text message) version of phishing. Instead of email, attackers use text messages to lure victims into providing sensitive data. Smishing messages may contain a link to a fraudulent website, or they may trick recipients into downloading malicious apps. In many cases, these messages will claim to be from a legitimate service, such as a delivery company, bank, or government institution, and will create a sense of urgency to prompt immediate action.
Smishing has become particularly prevalent due to the widespread use of smartphones, which are often less protected than desktop computers. Many people are not as cautious about SMS messages as they are about emails, making them more vulnerable to these kinds of attacks.
Why Awareness Matters: People are accustomed to receiving SMS messages from legitimate businesses, such as banks or delivery services, which makes it easier for attackers to disguise themselves. As more services rely on SMS for authentication or customer communication, being able to spot a suspicious message becomes essential. Avoid clicking on links in unexpected messages and verify the sender by contacting the company directly through official channels.
Vishing (Voice Phishing)
Vishing, or voice phishing, involves attackers making phone calls to deceive individuals into sharing personal information. Unlike phishing or smishing, vishing does not rely on written communication. Instead, attackers may pose as bank representatives, tech support agents, or even government officials, convincing victims to provide sensitive details over the phone.

Attackers often use sophisticated techniques, such as spoofing legitimate phone numbers, to make the call appear genuine. They may also create a sense of urgency, claiming that immediate action is required to prevent fraud or fix a technical issue.
Why Awareness Matters: With the increase in remote work and the reliance on phone-based customer service, vishing has become more widespread. It’s essential to remember that reputable organisations will never ask for sensitive information over the phone. If a call seems suspicious, it’s always best to hang up and contact the company directly using verified contact details.
Quishing (QR Code Phishing)
Quishing, or QR code phishing, is a newer form of attack where cybercriminals use QR codes to direct victims to malicious websites. As QR codes become more common—especially with the rise of contactless services and mobile payments—attackers are leveraging them as a phishing tool. A quishing attack might involve placing malicious QR codes in public places, such as posters, flyers, or menus, or even embedding them in phishing emails. When scanned, these codes direct the victim to a fraudulent website designed to steal their information or infect their device with malware.One of the challenges with quishing is that QR codes are opaque to the human eye. Unlike traditional phishing links, which can sometimes be scrutinised before clicking, QR codes are simply scanned with a mobile device, and the resulting link is opened automatically, making it harder for users to spot malicious intent.
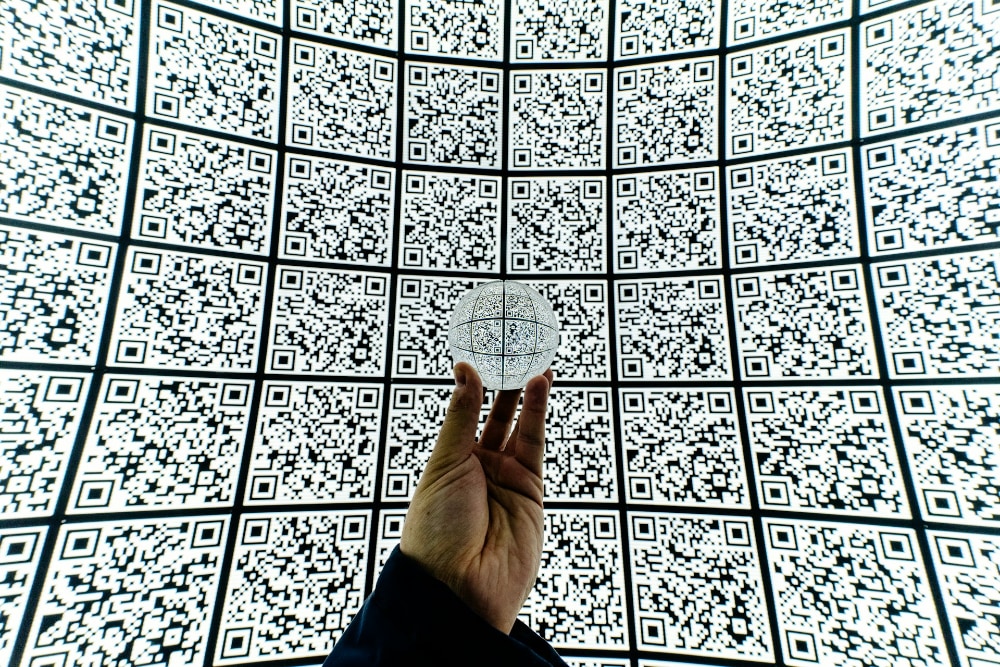
Why Awareness Matters: As QR codes become increasingly integrated into everyday life—whether in restaurants, public transport, or online services—people need to be aware of the risks they can pose. Always be cautious about scanning QR codes from unfamiliar or unexpected sources, and avoid using QR codes in unsolicited emails or messages.
2. Ransomware
Ransomware attacks have seen a dramatic rise in recent years, affecting everyone from small businesses to large multinational corporations. In these attacks, threat actors either encrypt a victim’s data, steal a victim’s sensitive data, or in most cases, do both. They then demand a ransom in exchange for the decryption key. Failure to pay often results in the permanent loss of data or its public release. The financial and reputational damage caused by such attacks can be terminal to businesses.
Why Awareness Matters: Knowing how ransomware works and understanding the best practices for data backup and protection can prevent these attacks from succeeding. Regularly updating software, ensuring strong password management, and being cautious about opening unknown attachments are critical steps in mitigating this threat.
3. Social Engineering
Social engineering attacks manipulate human psychology to trick individuals into divulging confidential information. These attacks often bypass technical security measures by exploiting human behaviour. Techniques can include impersonation, pretexting, and baiting, all of which rely on an individual’s trust or fear. Social engineering is a key tactic utilised by threat actors to manipulate the human factor into either installing malware, or divulging access credentials.
Why Awareness Matters: Cybersecurity training must include an emphasis on recognising the signs of social engineering. Knowing that these attacks rely on manipulating emotions—such as urgency, fear, or trust—can help individuals avoid becoming victims.
4. IoT Vulnerabilities
With the increasing adoption of the Internet of Things (IoT), more devices are connected to the internet than ever before. From smart thermostats to wearable fitness trackers, these devices provide convenience but often lack robust security measures, such as default, widely-known passwords. Hackers can exploit these vulnerabilities to gain access to networks and sensitive data.

Why Awareness Matters: As IoT devices become more integrated into our daily lives, it’s crucial to be aware of their security limitations. Regularly updating firmware, using strong and unique passwords, and understanding the risks associated with connected devices can help minimise potential vulnerabilities.5.
Remote Working Risks
The shift to remote working brought about by the COVID-19 pandemic has had a lasting impact on the workplace. While flexible working arrangements offer many benefits, they also introduce new cybersecurity challenges. Remote workers often use personal devices, unsecured home networks, and cloud-based platforms, all of which can be potential entry points for cyberattacks.
Why Awareness Matters: Employers and employees alike must understand the risks associated with remote working. Implementing Virtual Private Networks (VPNs), multi-factor authentication, and company-wide cybersecurity policies can help mitigate these risks.
Additionally, training staff to recognise potential threats in their home environment is key to maintaining security.
6. Supply Chain Attacks
Supply chain attacks are becoming an increasingly popular tactic for cybercriminals. These attacks target the weaker links in an organisation’s supply chain, such as vendors, third-party service providers, or contractors. By exploiting these partners, attackers can gain access to the primary organisation’s network.
Why Awareness Matters: Cybersecurity awareness must extend beyond internal operations. Businesses should ensure that all partners and vendors adhere to robust cybersecurity protocols. Regular audits and reviews of supply chain security measures can help identify potential vulnerabilities before they are exploited.
The Human Factor in Cybersecurity
Despite the technological sophistication of modern cyberattacks, humans remain the weakest link in the cybersecurity chain. According to a study by IBM, human error is responsible for 95% of cybersecurity breaches. Whether it’s falling for a phishing scam, using weak passwords, or failing to update software, simple mistakes can lead to devastating consequences.
This is where awareness becomes crucial. While it’s impossible to eliminate human error entirely, educating people about the risks and providing them with the tools to protect themselves can significantly reduce the chances of a breach. Awareness is the first line of defence against cyber threats.
Why Cybersecurity Awareness is Everyone’s Responsibility
One of the biggest misconceptions about cybersecurity is that it’s only the responsibility of IT departments or cybersecurity experts. In reality, cybersecurity is everyone’s responsibility. Whether you’re an employee, a student, or a home user, you play a critical role in protecting the data and systems you interact with.Here are some key reasons why cybersecurity awareness matters for everyone:
1. Preventing Data Breaches
Data breaches can have serious consequences, from financial losses to reputational damage. Personal data, financial information, and intellectual property are all valuable targets for cybercriminals. Being aware of the threats and knowing how to protect sensitive information can prevent breaches from occurring.
2. Protecting Personal Privacy
In an age where data is one of the most valuable commodities, protecting personal privacy is more important than ever. Cybercriminals can use stolen data for identity theft, fraud, or even blackmail. By understanding how data is collected, shared, and protected, individuals can take steps to safeguard their privacy.
3. Safeguarding Critical Infrastructure
Cyberattacks on critical infrastructure, such as power grids, water supply systems, and healthcare services, can have catastrophic consequences. These attacks are often designed to disrupt essential services, causing widespread chaos and endangering lives.
Cybersecurity awareness among employees working in these sectors is crucial to preventing such attacks.

4. Avoiding Financial Losses
Cybercrime is big business, and the financial impact of a successful attack can be enormous. From ransomware payments to the costs of recovering from a data breach, businesses and individuals can face significant financial losses. By staying informed about the latest threats and best practices, you can reduce the likelihood of becoming a victim.
5. Maintaining Business Continuity
For businesses, a successful cyberattack can be disastrous. Downtime, data loss, and damage to a company’s reputation can all threaten its survival. Cybersecurity awareness helps employees at all levels understand their role in maintaining business continuity. Simple actions, like following password protocols or reporting suspicious activity, can make all the difference.
Practical Steps to Improve Cybersecurity Awareness
Raising awareness about cybersecurity is not just about scaring people with the potential dangers. It’s about empowering them with the knowledge and tools they need to protect themselves and their organisations. Here are some practical steps that can be taken to improve cybersecurity awareness:
1. Regular Training
Cybersecurity training should be an ongoing process, not a one-time event. Regularly updated training sessions ensure that employees are aware of the latest threats and know how to respond. This can include phishing simulations, password management workshops, and sessions on secure browsing habits.
2. Clear Communication
Organisations should establish clear communication channels for reporting suspiciousactivity. Employees should feel comfortable reporting potential threats without fear of reprimand. A culture of openness and trust encourages proactive cybersecurity behaviour.

3. Cybersecurity Policies
Every organisation should have a comprehensive cybersecurity policy in place. This policy should outline best practices for password management, data handling, software updates, and incident reporting. Ensuring that all employees understand and follow these guidelines is key to maintaining a secure environment.
4. Use of Technology
While human awareness is crucial, technology also plays an essential role in cybersecurity. Tools such as antivirus software, firewalls, VPNs, and multi-factor authentication can provide an extra layer of protection. Educating individuals on how to use these tools effectively is a critical aspect of cybersecurity awareness.
5. Staying Informed
Cybersecurity is an ever-evolving field, with new threats emerging regularly. Staying informed about the latest trends, vulnerabilities, and best practices is essential for maintaining security. Following trusted cybersecurity news sources and participating in cybersecurity events can help keep individuals and organisations up to date.
You can find some more information about creating a cyber security culture in your SME here.
Conclusion
As Cybersecurity Month begins, let’s remember that awareness is the cornerstone of cyber defence. Whether you’re an individual looking to protect your personal information, a business owner securing your operations, or an employee contributing to your company’s security, staying informed and aware is the best way to combat cyber threats.
At SOS Intelligence, we’re committed to promoting cybersecurity awareness and helping individuals and organisations stay safe in an increasingly digital world. This month, take the time to educate yourself and those around you on the importance of cybersecurity.
Together, we can build a safer online environment for everyone.
If you’d like to speak to one of the team to learn about how we can make you sleep easier at night, please get in touch here. Thank you!
Photos by Kenny Eliason, freestocks, Mitya Ivanov Jakub Żerdzicki Nicolas HIPPERT Pavan Trikutam.

