To kick off our OSINT series, here’s a guide to key terms in open-source intelligence, organised into categories. These will lay the foundation for understanding OSINT’s role in gathering insights:
Types of Intelligence
- Open-Source Intelligence (OSINT): Intelligence gathered from publicly accessible sources, including online and offline materials. OSINT is essential in cybersecurity, threat intelligence, and digital investigations.
- SOCMINT (Social Media Intelligence): Intelligence derived from social media, analysing public posts, trends, and interactions. SOCMINT provides real-time insights but requires careful handling of privacy and ethical considerations.
- HUMINT (Human Intelligence): Information collected through direct human interaction, such as interviews, surveys, or conversations. HUMINT is often used alongside OSINT to validate findings.
- TECHINT (Technical Intelligence): Intelligence from analysing technical data, like system specifications, software tools, and network structures. It’s valuable for understanding technical aspects of targets or threats.

Layers of the Internet
- Surface Web: The portion of the internet accessible through standard search engines (e.g., Google), including publicly available websites, blogs, and social media—about 5-10% of online content.
- Deep Web: Content not indexed by search engines, such as academic databases, private files, and subscription-based resources. Unlike the Dark Web, it’s mostly used for legitimate purposes.
- Dark Web: A hidden layer of the internet accessible only through specialised software (e.g., Tor). Known for its anonymity, it hosts both legal and illegal activities.

Data and Information Gathering Techniques
- Footprinting: The initial OSINT phase, where information is gathered to understand a target’s structure, such as network details, employee information, and online presence.
- Data Scraping: Extracting large volumes of data from websites or online sources for analysis and intelligence purposes.
- Social Engineering: Manipulating individuals to divulge confidential information by exploiting psychological tactics rather than technical hacking.
Technical Aspects and Tools
- Metadata: Data that provides information about other data. In OSINT, metadata can reveal details such as the author of a document, creation date, and location.
- Geolocation: Determining a device or individual’s physical location based on data such as IP addresses, GPS, or social media posts.
- API (Application Programming Interface): A set of rules enabling different software to communicate. APIs are often used in OSINT to retrieve data from various platforms.
- Encryption: The method of encoding information to prevent unauthorised access. It’s a crucial tool for protecting sensitive data in OSINT operations.

Cybersecurity and Threat Analysis
- Threat Intelligence: Information about threats and threat actors, helping organisations prepare for potential cyberattacks.
- Attribution: Identifying the source of a cyberattack or malicious activity, often using OSINT techniques to trace back to the origin.
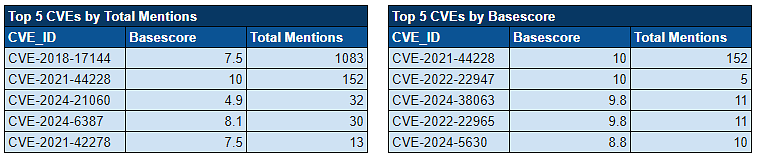
- Vulnerability Assessment: Evaluating a system for security weaknesses that could be exploited by threat actors, with OSINT uncovering publicly available information about potential vulnerabilities.
- Digital Footprint: The trail of data left behind while using the internet, including sites visited, emails sent, and online information submitted.
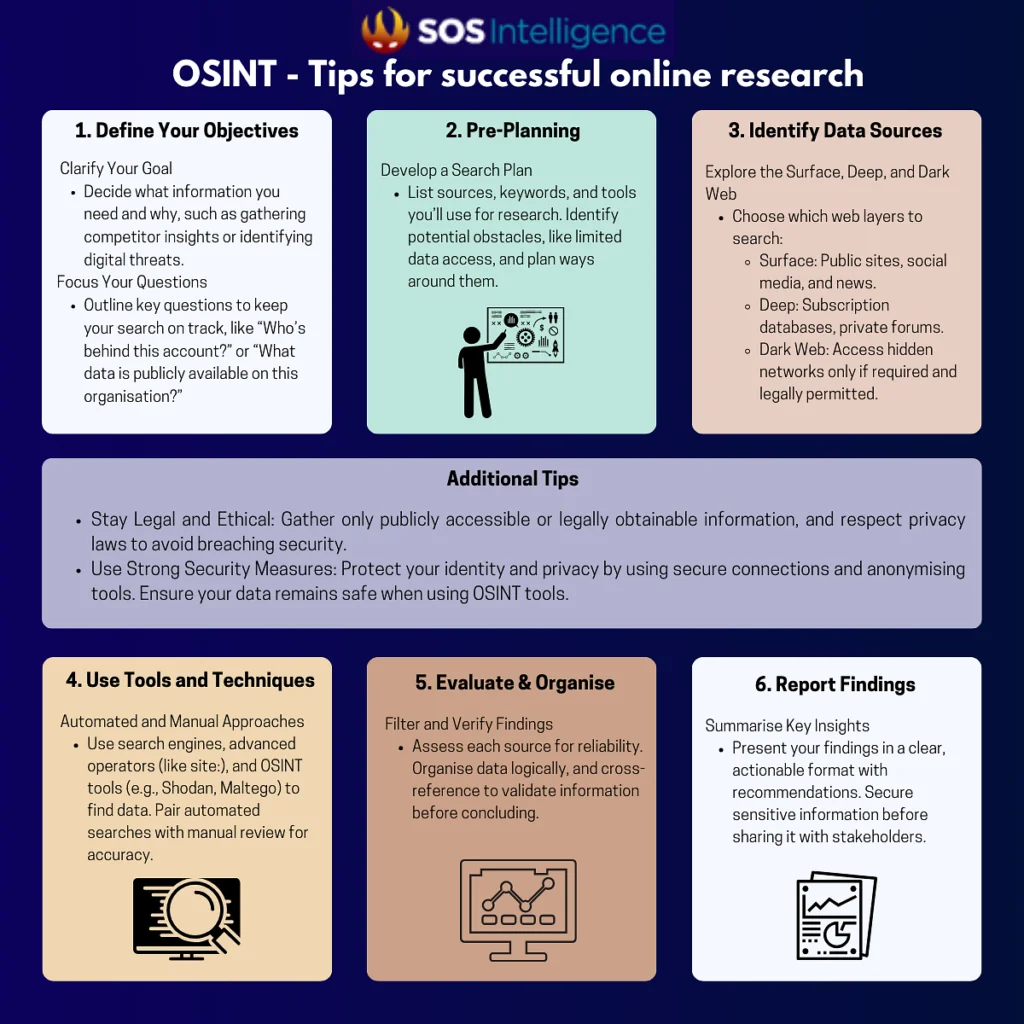
Also, don’t miss this post on the basics of OSINT.
Photos by Thomas Jensen Stellan Johansson Gregoire Jeanneau on Unsplash






































Recent Comments