In today’s fast-paced digital age, businesses are more connected than ever before. While this connectivity has created countless growth opportunities, it has also introduced new vulnerabilities. Cyber threats have evolved in sophistication, making them a critical concern for businesses of all sizes.
Small and medium-sized enterprises (SMEs) are particularly attractive targets for cybercriminals. Unlike larger corporations, which often have dedicated security teams and robust defences in place, SMEs frequently lack the resources to protect themselves adequately. This perception of vulnerability makes them an enticing target for attackers.
According to the Federation of Small Businesses (FSB), cybercrime costs the UK economy around £4.5 billion annually, with the average cost of an attack on a small business estimated to be around £1,300 per victim. For an SME, a cyberattack can lead to not only significant financial losses but also loss of customer trust, reputational damage, and even the risk of going out of business.
As a business owner, it’s essential to be aware of the common types of cyber threats and how to protect your business. In this blog, we’ll explore the top five cyber threats facing SMEs, share real-world examples of businesses that have been impacted, and provide actionable tips on how to identify and prevent these attacks.
1. Phishing Attacks
What is Phishing?
Phishing is a form of social engineering that involves cybercriminals pretending to be trusted entities to trick individuals into revealing sensitive information such as passwords, bank details, or personal data. These attacks are most commonly conducted via email but can also occur through text messages (smishing) or phone calls (vishing). When such attacks are targeted at a specific person within a company, often someone in a senior or sensitive role, they are referred to as spear phishing.
Phishing emails often contain malicious links or attachments. When an unsuspecting employee clicks on a link or downloads an attachment, they might inadvertently provide access to sensitive company data or install malware on their device.
Real-Life Example: The WADA Attack
In 2016, the World Anti-Doping Agency (WADA) became the target of a sophisticated phishing attack. Hackers posed as WADA officials and tricked employees into revealing login credentials. These credentials were then used to access confidential athlete information, which was subsequently leaked. The damage caused by this breach not only harmed WADA’s reputation but also disrupted trust in global anti-doping efforts.
How to Identify Phishing:
- Suspicious Email Addresses: Phishing emails may appear to come from legitimate sources, but a close inspection of the sender’s email address often reveals small inconsistencies, such as an extra character or unusual domain name.
- Urgency and Fear Tactics: Many phishing emails create a sense of urgency or fear. For example, they may claim your account will be suspended unless you take immediate action.
- Unexpected Attachments or Links: Phishing emails may ask recipients to open attachments or click on links. Always hover over links to verify their destination before clicking.
How to Protect Your SME:
- Implement Two-Factor Authentication (2FA): 2FA adds an extra layer of security by requiring users to provide two forms of identification before accessing accounts. This reduces the risk of compromised passwords.
- Ongoing Employee Training: Regularly educate your employees about the risks of phishing. Make sure they know how to identify suspicious emails and what to do if they receive one.
- Advanced Email Security: Use email filtering tools that block or flag suspicious messages before they reach your employees’ inboxes.
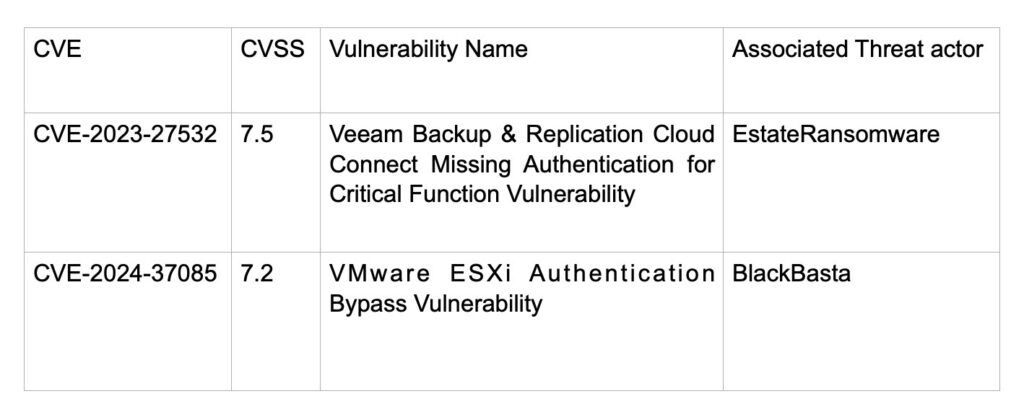
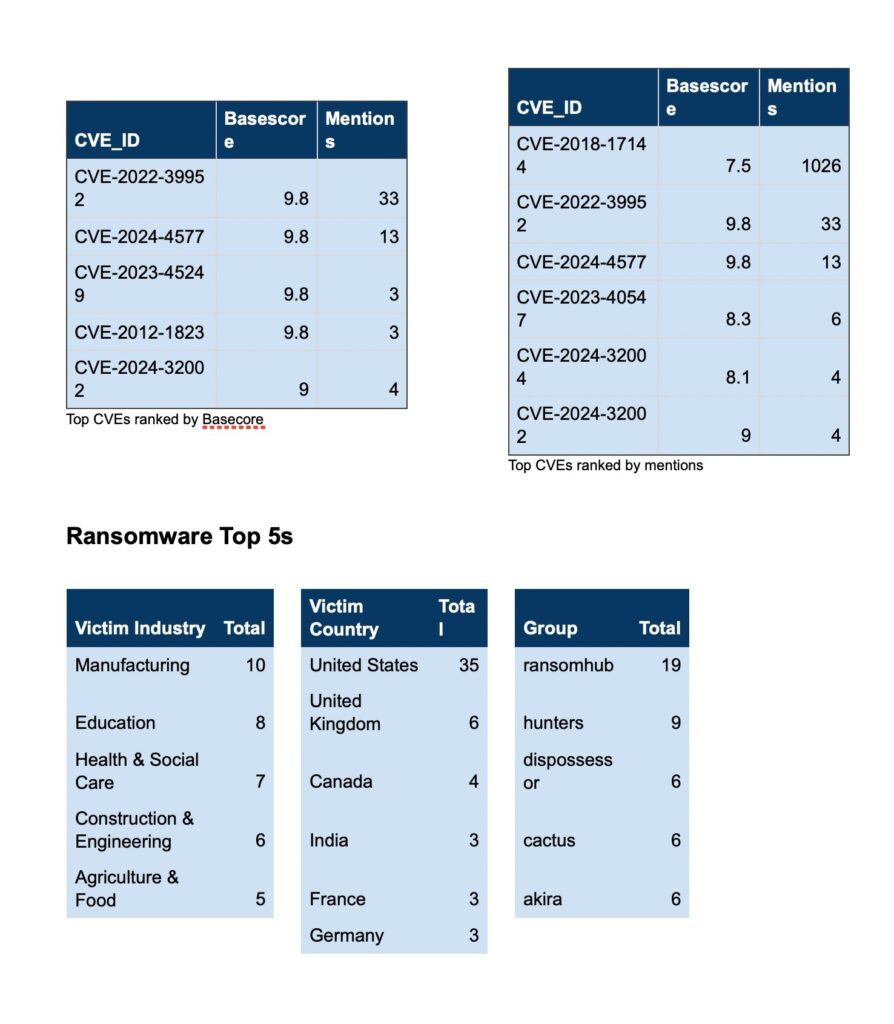
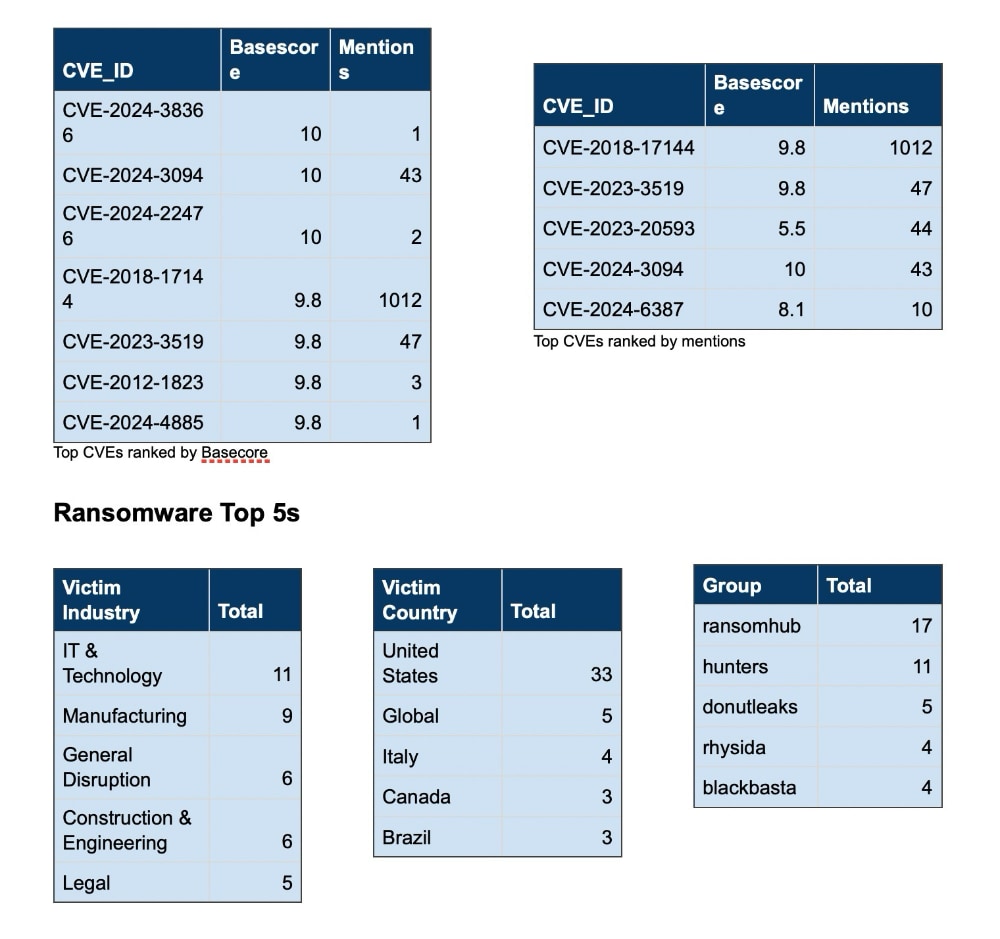
2. Ransomware
What is Ransomware?
Ransomware is a type of malicious software that locks or encrypts a victim’s data, rendering it inaccessible until a ransom is paid. Cybercriminals typically demand payment in cryptocurrencies, which are harder to trace, and often provide a tight deadline for payment to pressure victims.

For SMEs, ransomware can be devastating. In addition to the ransom itself, businesses can face operational downtime, loss of sensitive data, and a hit to their reputation. Moreover, there is no guarantee that paying the ransom will lead to the recovery of your data.
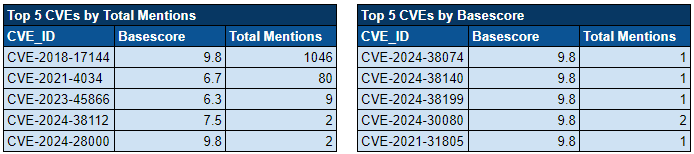
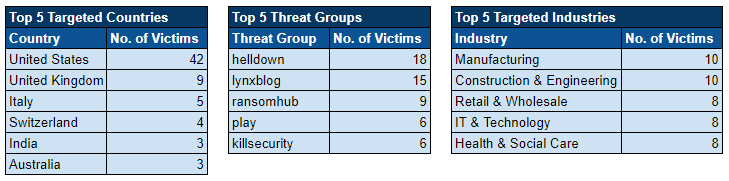
In recent years, the majority of ransomware threat actors have moved to a double extortion method, whereby not only do they encrypt your data, but they also threaten to release it to the public through their victim-shaming blogs. We are now also beginning to see instances where threat actors rely solely on this threat of data publication, rather than data encryption.
Real-Life Example: The WannaCry Attack
In 2017, the WannaCry ransomware attack swept across the globe, affecting more than 200,000 computers in over 150 countries. One of the most notable victims was the NHS in the UK, which faced widespread disruption as critical medical systems became inoperable. WannaCry exploited a vulnerability in older versions of Microsoft Windows, and while a patch had been released, many organisations had not yet applied it.
The total financial impact of WannaCry was estimated to be in the billions, with businesses around the world incurring significant downtime and recovery costs.
How to Identify a Ransomware Attack:
- Files Become Inaccessible: One of the most obvious signs of a ransomware attack is that you are suddenly unable to access your files or data.
- Ransom Note: Ransomware attacks often display a message explaining that your files have been encrypted and demanding payment for their release.
- Unusual Network Activity: You may notice strange spikes in network traffic as ransomware spreads through your system, attempting to encrypt all connected devices.
How to Protect Your SME:
- Backup Critical Data: Regularly back up your data and ensure that backups are stored offline or in a secure cloud service. This way, if a ransomware attack occurs, you can restore your data without paying the ransom.
- Patch and Update Software: Ensure all systems and software are up-to-date. Many ransomware attacks exploit known vulnerabilities that can be patched through regular updates.
- Endpoint Security Solutions: Install advanced antivirus and anti-malware software that can detect and block ransomware before it causes damage.
3. Malware
What is Malware?
Malware is an umbrella term used to describe any malicious software designed to disrupt, damage, or gain unauthorised access to a computer system. Types of malware include viruses, worms, trojans, spyware, and adware.
Once malware infiltrates a system, it can steal data, monitor user activity, install additional harmful software, or even render systems inoperable. For SMEs, a malware attack can result in lost productivity, compromised customer data, and long-term damage to your brand’s reputation.
Real-Life Example: The NotPetya Attack
NotPetya was initially thought to be ransomware, but its true intent was far more destructive. In June 2017, the malware spread across organisations globally, severely impacting businesses like shipping giant Maersk, which faced significant operational downtime and financial losses as its systems were brought to a halt. The attack encrypted critical files and disrupted supply chains, costing Maersk an estimated £300 million.
NotPetya also highlights another significant cyber-security concern: supply-chain attacks. The malware had originated from the Ukrainian company Intellect Service, which supplied tax software. Threat actors breached the company and configured their software updater to download the malware to anyone using the software, which occurred when the latest software update was pushed. This highlights the need to properly consider not only your risk but third-party risk as well.
How to Identify Malware:
- Sluggish Performance: If your computers or network are unusually slow, this could be a sign that malware is consuming system resources.
- Pop-Up Ads: Malware infections are often accompanied by a barrage of unwanted pop-up ads, even when you’re not browsing the web.
- System Crashes: Frequent crashes or the appearance of the “blue screen of death” could indicate that your system has been compromised.
How to Protect Your SME:
- Install and Update Antivirus Software: Ensure that all company devices are equipped with up-to-date antivirus software. Schedule regular scans to identify and remove malware.
- Limit Software Downloads: Only allow trusted employees to install or download software to prevent the introduction of malware from suspicious sources.
- Monitor Network Traffic: Keep an eye on your network for unusual spikes in data usage, which could be a sign of malware communicating with external servers.
4. Insider Threats
What are Insider Threats?
Insider threats come from within your organisation and are caused by employees, contractors, or anyone with legitimate access to your systems. These individuals can either intentionally or unintentionally compromise your data and security. Insider threats can be difficult to detect because they exploit trusted access.
Real-Life Example: Tesla’s Insider Sabotage

In 2018, Tesla faced an insider threat when a disgruntled employee deliberately sabotaged the company’s systems. The employee altered the company’s manufacturing operating system and leaked confidential data to third parties. Tesla’s CEO, Elon Musk, publicly confirmed the damage caused by the incident, which affected the company’s operations and intellectual property.
How to Identify Insider Threats:
- Unusual Access Patterns: If an employee is accessing files or systems they don’t usually use, this could be a sign of an insider threat.
- Data Downloads: Sudden spikes in data downloads, especially involving sensitive information, can indicate malicious activity.
- Employee Behaviour: Employees exhibiting signs of dissatisfaction or frustration could potentially become insider threats.
How to Protect Your SME:
- Role-Based Access Control (RBAC): Limit access to data based on an employee’s role and responsibilities. Employees should only have access to the information necessary for their job.
- Regular Audits: Conduct routine audits of system access and file downloads. This can help identify unusual patterns of behaviour that may indicate an insider threat.
- Encourage Employee Reporting: Create a culture where employees feel comfortable reporting suspicious behaviour, without fear of retribution.
5. Distributed Denial of Service (DDoS) Attacks
What is a DDoS Attack?
A Distributed Denial of Service (DDoS) attack occurs when multiple compromised systems flood a target, such as a website or online service, with an overwhelming amount of traffic. The sheer volume of requests causes the target to become slow, unresponsive, or even crash altogether.
While DDoS attacks don’t typically result in data theft, they can cause significant operational disruptions. For SMEs that rely on online services, even a temporary outage can lead to lost revenue, frustrated customers, and long-term reputational damage.
Real-Life Example: The Dyn DNS Attack
In 2016, Dyn, a major provider of DNS services, was hit by a massive DDoS attack that affected major websites such as Twitter, Spotify, and Netflix. The attack, which was conducted using a botnet made up of Internet of Things (IoT) devices, disrupted services for several hours, highlighting the vulnerability of DNS infrastructure and the far-reaching impact of DDoS attacks.
How to Identify a DDoS Attack:
- Slow or Unresponsive Website: If your website becomes unusually slow or users report difficulty accessing it, this could be the result of a DDoS attack.
- Spike in Traffic: A sudden and unexpected increase in traffic, especially if it comes from unknown or foreign sources, is a common indicator of a DDoS attack.
- Service Outages: Repeated service interruptions or crashes can point to a sustained DDoS assault.
How to Protect Your SME:
- Use a CDN: Content Delivery Networks (CDNs) distribute traffic across multiple servers, reducing the impact of DDoS attacks by ensuring that no single server is overwhelmed.
- Invest in DDoS Mitigation Services: There are dedicated DDoS mitigation tools and services that can detect abnormal traffic patterns and block malicious requests before they reach your network.
- Firewalls and Load Balancers: Use Web Application Firewalls (WAFs) and load balancers to filter incoming traffic, block malicious IP addresses, and distribute the load more effectively across servers.
Conclusion: Building a Resilient Cybersecurity Strategy
The risks of cyberattacks are real, and for SMEs, the consequences can be especially severe. By understanding the top cyber threats—phishing, ransomware, malware, insider threats, and DDoS attacks—business owners can take proactive steps to secure their operations.
Cybersecurity is not just a technical issue but a fundamental part of business resilience. Implementing strong security measures, providing ongoing employee training, and fostering a culture of cybersecurity awareness will go a long way in reducing the risk of cyberattacks.
Ultimately, it’s not about if your business will be targeted but when. Taking the time to assess your vulnerabilities and enhance your security protocols now will save you time, money, and reputation in the long run. The best time to protect your business is today.
Read our first post in this series here > What every SME needs to know.
Need Help?
If you don’t know about a threat, you cannot act. SOS Intelligence can be your eyes and ears on the dark web, providing digital risk monitoring to make sure you have the right intelligence, when you need it, to take action to protect your business. Click here to book a demo.
Photos by FlyD , Stephen Phillips – Hostreviews.co.uk, Michael Geiger on Unsplash.










Recent Comments