Plexal has announced the 108 cyber startups joining the Cyber Runway accelerator and we are delighted to have been chosen!
Cyber Runway is the UK’s most diverse community of cyber founders and entrepreneurs.
Cyber Runway has been designed to address some of the biggest challenges facing cybersecurity, such as diversity and inclusion and regional representation, and support the most promising innovators at various stages of growth.
The full membership list confirms that Cyber Runway will not only be the largest cyber startup accelerator in the UK, but the most diverse community of cyber founders in the country.
The cohorts are solving challenges like ransomware, cyber fraud, cyber-physical threats to critical national infrastructure, cloud security, improving threat intelligence and boosting education using emerging technologies such as AI, quantum and cloud security.
45% of Cyber Runway members are female-led startups and 52% are run by founders from black, ethnic or minority backgrounds.
You can see a list of Grow members including us here.
Plexal has ensured inclusivity is at the heart of Cyber Runway by including under-represented groups in the design and delivery of the programme. Members will also have access to a diverse mentor pool of investors and industry experts.
50% of member companies are based outside of London and the South East of England. From Ashford to Yeovil, members and their teams are based across the country and Cyber Runway will be delivered in person and virtually to maximise nationwide reach.
The Cyber Runway membership represents some of the most innovative and high-potential cyber startups currently operating in the UK. Members include scaleups such as CybSafe, which raised £5m earlier this year for its security awareness software, SECQAI, which uses quantum technology and AI to combat cyber threats, Yorkshire-based Bob’s Business, which delivers cyber training, insurtech startup Regulativ.ai, which aims to disrupt cyber regulatory compliance, and Hack The Box, which raised £7m in April for its online cybersecurity training platform.

Cyber Runway programme
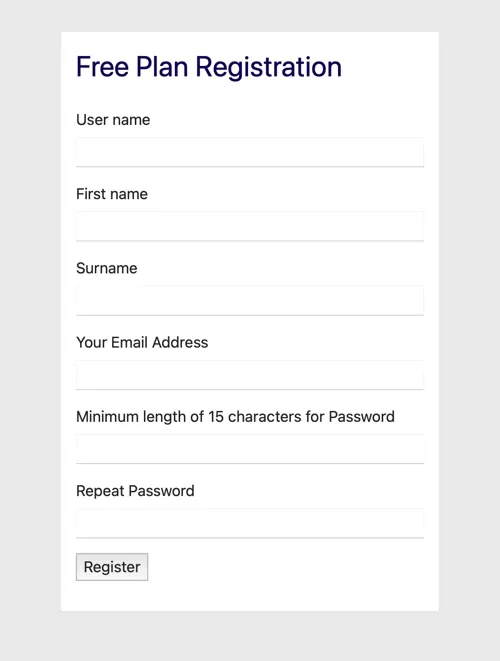
Backed by the Department for Digital, Culture, Media and Sport and delivered by Plexal in partnership with CyLon, Deloitte and CSIT (the Centre for Secure Information Technologies), Cyber Runway will be an intensive six-month programme. Three distinct streams will deliver dedicated curricula for cyber startups based on their growth phase: Launch, Grow and Scale.
Launch: 20 entrepreneurs will get support with launching their business, building a minimum viable product and creating a network.
Grow: 68 startups and SMEs will get business support to help them address their growing pains, access funding and achieve commercial success.
Scale: 20 scaleups will access support (including 1:1 mentoring) to help them grow rapidly in the UK and around the world.
Cyber Runway has replaced and consolidated three DCMS-funded programmes: HutZero, Cyber 101 and Tech Nation’s cyber accelerator for startups.
The accelerator is designed to strengthen the UK’s cyber ecosystem and accelerate the growth of a new generation of breakthrough cyber startups to improve national security, stimulate innovation and drive economic growth.
Cyber Runway: member benefits
The 108 member companies will receive:
- business masterclasses (both virtual and in person)
- mentoring, engineering support from CSIT and access to CSIT’s data and testing centre
- technical product development support
- opportunities to connect with international cyber hubs
- regional events
- connections to investors and corporates to fuel growth
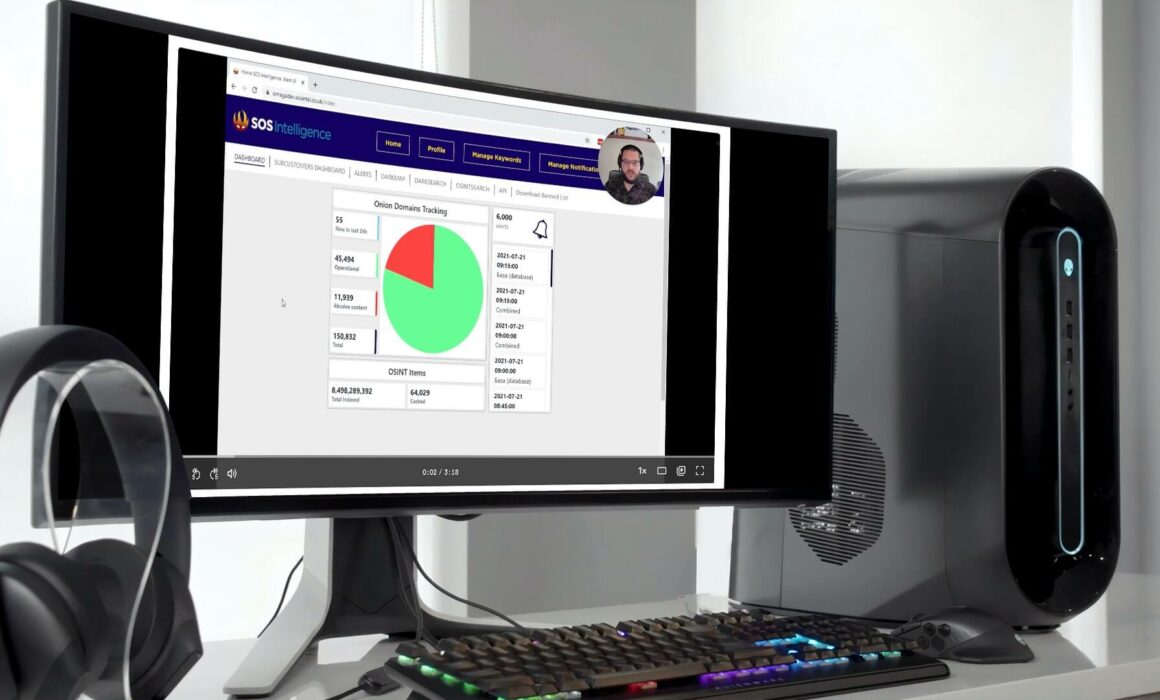
“We are delighted to have been selected to be a part of the Cyber Runway accelerator programme, we are excited to be participating in the excellent programme and to network with fellow cohorts. The Plexal team has put a lot of hard work into the programme and it shows. Many thanks to the team for making us feel so welcome.”
Amir Hadzipasic, CEO and Founder SOS Intelligence
“This is a golden age for the UK cyber startup ecosystem. Cyber startups are attracting record levels of investment and both the government and global tech giants are coming to British cyber companies to adopt emerging cyber technologies. The scale of Cyber Runway is testament to the enormous potential within the cyber startup community and will help stimulate the supply of innovative cyber solutions that will be needed by the economy and society.
However, Cyber Runway is also specifically designed to address some of the challenges facing cyber startups as they scale. Our three programmes will connect cyber founders to the mentors, investors and corporates they need to accelerate their growth and access diverse talent. This is a significant moment for UK cyber and I have every confidence that the collaboration between the government and the private sector to create Cyber Runway will make the cyber ecosystem more successful, innovative and inclusive.”
Saj Huq, director of innovation at Plexal.
For more information on SOS Intelligence, please schedule a demo here.
















Recent Comments