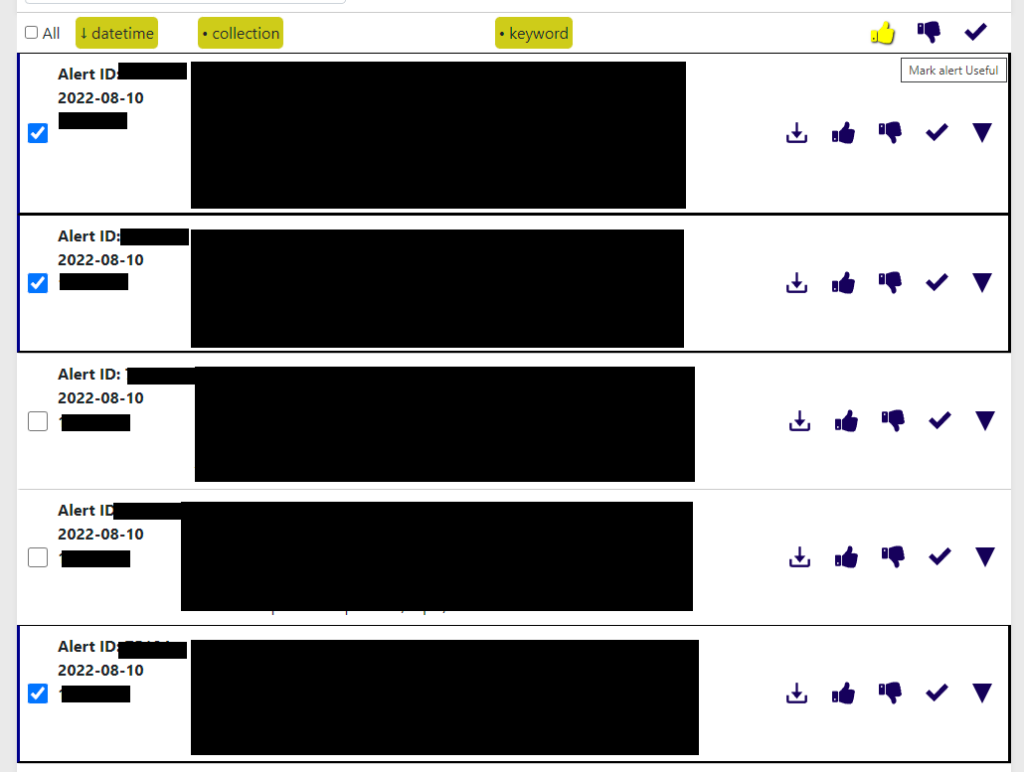
This weekly blog post is from via our unique intelligence collection pipelines. We are your eyes and ears online, including the Dark Web.
There are thousands of vulnerability discussions each week. SOS Intelligence gathers a list of the most discussed Common Vulnerabilities and Exposures (CVE) online for the previous week.
We make every effort to ensure the accuracy of the data presented. As this is an automated process some errors may creep in.
If you are feeling generous please do make us aware of anything you spot, feel free to follow us on Twitter @sosintel and DM us. Thank you!
1. CVE-2022-20259
In Telephony, there is a possible leak of ICCID and EID due to a missing permission check. This could lead to local information disclosure with no additional execution privileges needed. User interaction is not needed for exploitation.Product: AndroidVersions: Android-13Android ID: A-221431393
https://nvd.nist.gov/vuln/detail/CVE-2022-20259
2. CVE-2022-2610
Insufficient policy enforcement in Background Fetch in Google Chrome prior to 104.0.5112.79 allowed a remote attacker to leak cross-origin data via a crafted HTML page.
https://nvd.nist.gov/vuln/detail/CVE-2022-2610
3. CVE-2021-33646
The th_read() function doesn’t free a variable t->th_buf.gnu_longname after allocating memory, which may cause a memory leak.
https://nvd.nist.gov/vuln/detail/CVE-2021-33646
4. CVE-2021-33645
The th_read() function doesn’t free a variable t->th_buf.gnu_longlink after allocating memory, which may cause a memory leak.
https://nvd.nist.gov/vuln/detail/CVE-2021-33645
5. CVE-2020-12720
vBulletin before 5.5.6pl1, 5.6.0 before 5.6.0pl1, and 5.6.1 before 5.6.1pl1 has incorrect access control.
https://nvd.nist.gov/vuln/detail/CVE-2020-12720
6. CVE-2022-24086
Adobe Commerce versions 2.4.3-p1 (and earlier) and 2.3.7-p2 (and earlier) are affected by an improper input validation vulnerability during the checkout process. Exploitation of this issue does not require user interaction and could result in arbitrary code execution.
https://nvd.nist.gov/vuln/detail/CVE-2022-24086
7. CVE-2022-30190
Microsoft Windows Support Diagnostic Tool (MSDT) Remote Code Execution Vulnerability.
https://nvd.nist.gov/vuln/detail/CVE-2022-30190
8. CVE-2022-1215
A format string vulnerability was found in libinput
https://nvd.nist.gov/vuln/detail/CVE-2022-1215
9. CVE-2022-30075
Microsoft Windows Support Diagnostic Tool (MSDT) Remote Code Execution Vulnerability.
https://nvd.nist.gov/vuln/detail/CVE-2022-30075
10. CVE-2022-24087
Adobe Commerce versions 2.4.3-p1 (and earlier) and 2.3.7-p2 (and earlier) are affected by an improper input validation vulnerability during the checkout process. Exploitation of this issue does not require user interaction and could result in arbitrary code execution.
https://nvd.nist.gov/vuln/detail/CVE-2022-24087






Recent Comments