Home » SOS Intelligence » Page 3
This weekly blog post is from via our unique intelligence collection pipelines. We are your eyes and ears online, including the Dark Web.
There are thousands of vulnerability discussions each week. SOS Intelligence gathers a list of the most discussed Common Vulnerabilities and Exposures (CVE) online for the previous week.
We make every effort to ensure the accuracy of the data presented. As this is an automated process some errors may creep in.
If you are feeling generous please do make us aware of anything you spot, feel free to follow us on Twitter @sosintel and DM us. Thank you!
1. CVE-2023-24709
An issue found in Paradox Security Systems IPR512 allows attackers to cause a denial of service via the login.html and login.xml parameters.
https://nvd.nist.gov/vuln/detail/CVE-2023-24709
2. CVE-2023-6246
A heap-based buffer overflow was found in the __vsyslog_internal function of the glibc library. This function is called by the syslog and vsyslog functions. This issue occurs when the openlog function was not called, or called with the ident argument set to NULL, and the program name (the basename of argv[0]) is bigger than 1024 bytes, resulting in an application crash or local privilege escalation. This issue affects glibc 2.36 and newer.
https://nvd.nist.gov/vuln/detail/CVE-2023-6246
3. CVE-2023-38606
This issue was addressed with improved state management. This issue is fixed in macOS Monterey 12.6.8, iOS 15.7.8 and iPadOS 15.7.8, iOS 16.6 and iPadOS 16.6, tvOS 16.6, macOS Big Sur 11.7.9, macOS Ventura 13.5, watchOS 9.6. An app may be able to modify sensitive kernel state. Apple is aware of a report that this issue may have been actively exploited against versions of iOS released before iOS 15.7.1.
https://nvd.nist.gov/vuln/detail/CVE-2023-38606
4. CVE-2023-46805
An authentication bypass vulnerability in the web component of Ivanti ICS 9.x, 22.x and Ivanti Policy Secure allows a remote attacker to access restricted resources by bypassing control checks.
https://nvd.nist.gov/vuln/detail/CVE-2023-46805
5. CVE-2023-32434
An integer overflow was addressed with improved input validation. This issue is fixed in watchOS 9.5.2, macOS Big Sur 11.7.8, iOS 15.7.7 and iPadOS 15.7.7, macOS Monterey 12.6.7, watchOS 8.8.1, iOS 16.5.1 and iPadOS 16.5.1, macOS Ventura 13.4.1. An app may be able to execute arbitrary code with kernel privileges. Apple is aware of a report that this issue may have been actively exploited against versions of iOS released before iOS 15.7.
https://nvd.nist.gov/vuln/detail/CVE-2023-32434
6. CVE-2020-1472
An elevation of privilege vulnerability exists when an attacker establishes a vulnerable Netlogon secure channel connection to a domain controller, using the Netlogon Remote Protocol (MS-NRPC). An attacker who successfully exploited the vulnerability could run a specially crafted application on a device on the network.
To exploit the vulnerability, an unauthenticated attacker would be required to use MS-NRPC to connect to a domain controller to obtain domain administrator access.
Microsoft is addressing the vulnerability in a phased two-part rollout. These updates address the vulnerability by modifying how Netlogon handles the usage of Netlogon secure channels.
For guidelines on how to manage the changes required for this vulnerability and more information on the phased rollout, see How to manage the changes in Netlogon secure channel connections associated with CVE-2020-1472 (updated September 28, 2020).
When the second phase of Windows updates become available in Q1 2021, customers will be notified via a revision to this security vulnerability. If you wish to be notified when these updates are released, we recommend that you register for the security notifications mailer to be alerted of content changes to this advisory. See Microsoft Technical Security Notifications.
https://nvd.nist.gov/vuln/detail/CVE-2020-1472
7. CVE-2023-41990
The issue was addressed with improved handling of caches. This issue is fixed in tvOS 16.3, iOS 16.3 and iPadOS 16.3, macOS Monterey 12.6.8, macOS Big Sur 11.7.9, iOS 15.7.8 and iPadOS 15.7.8, macOS Ventura 13.2, watchOS 9.3. Processing a font file may lead to arbitrary code execution. Apple is aware of a report that this issue may have been actively exploited against versions of iOS released before iOS 15.7.1.
https://nvd.nist.gov/vuln/detail/CVE-2023-41990
8. CVE-2024-21888
A privilege escalation vulnerability in web component of Ivanti Connect Secure (9.x, 22.x) and Ivanti Policy Secure (9.x, 22.x) allows a user to elevate privileges to that of an administrator.
https://nvd.nist.gov/vuln/detail/CVE-2024-21888
9. CVE-2023-32435
A memory corruption issue was addressed with improved state management. This issue is fixed in macOS Ventura 13.3, Safari 16.4, iOS 16.4 and iPadOS 16.4, iOS 15.7.7 and iPadOS 15.7.7. Processing web content may lead to arbitrary code execution. Apple is aware of a report that this issue may have been actively exploited against versions of iOS released before iOS 15.7.
https://nvd.nist.gov/vuln/detail/CVE-2023-32435
10. CVE-2024-21887
A command injection vulnerability in web components of Ivanti Connect Secure (9.x, 22.x) and Ivanti Policy Secure (9.x, 22.x) allows an authenticated administrator to send specially crafted requests and execute arbitrary commands on the appliance.
https://nvd.nist.gov/vuln/detail/CVE-2024-21887
Two new vulnerabilities have been disclosed by Ivanti, relating to their Connect Secure, Policy Secure and Neurons for ZTA products and services.
Ivanti Connect Secure & Ivanti Policy Secure
CVSS: 8.8 HIGH
Ivanti has disclosed a further vulnerability affecting their Connect Secure and Policy Secure solutions. Impacting all currently supported versions (9.x and 22.x), the vulnerability allows a user (malicious or otherwise) to elevate their current privileges to that of an administrator.
Ivanti Connect Secure, Ivanti Policy Secure & Ivanti Neurons for ZTA
CVSS: 8.2 HIGH
A server-side vulnerability exists in the SAML component of Ivanti Connect Secure, Ivanti Policy Secure & Ivanti Neurons for ZTA. When exploited, a threat actor could access certain restricted resources without needing to authenticate.
While no threat actor use of CVE-2024-21888 has yet been discovered, there has been limited, targeted use of CVE-2024-21893. Following the disclosure of these vulnerabilities, exploitation of impacted services is suspected to increase. Therefore, it is vital that the affected services are fully patched and updated to mitigate any risks.
The release of these vulnerabilities follows Ivanti’s research into vulnerabilities disclosed earlier in the month, CVE-2023-46805 and CVE-2024-21887 (previously reported here). Given the volume of vulnerabilities coming from Ivanti at this time, it is expected that threat actors will put an increased focus on identifying more in order to exploit vulnerable users.
This weekly blog post is from via our unique intelligence collection pipelines. We are your eyes and ears online, including the Dark Web.
There are thousands of vulnerability discussions each week. SOS Intelligence gathers a list of the most discussed Common Vulnerabilities and Exposures (CVE) online for the previous week.
We make every effort to ensure the accuracy of the data presented. As this is an automated process some errors may creep in.
If you are feeling generous please do make us aware of anything you spot, feel free to follow us on Twitter @sosintel and DM us. Thank you!
1. CVE-2021-44228
Apache Log4j2 2.0-beta9 through 2.15.0 (excluding security releases 2.12.2, 2.12.3, and 2.3.1) JNDI features used in configuration, log messages, and parameters do not protect against attacker controlled LDAP and other JNDI related endpoints. An attacker who can control log messages or log message parameters can execute arbitrary code loaded from LDAP servers when message lookup substitution is enabled. From log4j 2.15.0, this behavior has been disabled by default. From version 2.16.0 (along with 2.12.2, 2.12.3, and 2.3.1), this functionality has been completely removed. Note that this vulnerability is specific to log4j-core and does not affect log4net, log4cxx, or other Apache Logging Services projects.
https://nvd.nist.gov/vuln/detail/CVE-2021-44228
2. CVE-2021-43008
Improper Access Control in Adminer versions 1.12.0 to 4.6.2 (fixed in version 4.6.3) allows an attacker to achieve Arbitrary File Read on the remote server by requesting the Adminer to connect to a remote MySQL database.
https://nvd.nist.gov/vuln/detail/CVE-2021-43008
3. CVE-2020-16040
Insufficient data validation in V8 in Google Chrome prior to 87.0.4280.88 allowed a remote attacker to potentially exploit heap corruption via a crafted HTML page.
https://nvd.nist.gov/vuln/detail/CVE-2020-16040
4. CVE-2022-22620
A use after free issue was addressed with improved memory management. This issue is fixed in macOS Monterey 12.2.1, iOS 15.3.1 and iPadOS 15.3.1, Safari 15.3 (v. 16612.4.9.1.8 and 15612.4.9.1.8). Processing maliciously crafted web content may lead to arbitrary code execution. Apple is aware of a report that this issue may have been actively exploited..
https://nvd.nist.gov/vuln/detail/CVE-2022-22620
5. CVE-2023-49070
Pre-auth RCE in Apache Ofbiz 18.12.09.
It’s due to XML-RPC no longer maintained still present.
This issue affects Apache OFBiz: before 18.12.10.
Users are recommended to upgrade to version 18.12.10
https://nvd.nist.gov/vuln/detail/CVE-2023-49070
6. CVE-2014-6271
GNU Bash through 4.3 processes trailing strings after function definitions in the values of environment variables, which allows remote attackers to execute arbitrary code via a crafted environment, as demonstrated by vectors involving the ForceCommand feature in OpenSSH sshd, the mod_cgi and mod_cgid modules in the Apache HTTP Server, scripts executed by unspecified DHCP clients, and other situations in which setting the environment occurs across a privilege boundary from Bash execution, aka “ShellShock.” NOTE: the original fix for this issue was incorrect; CVE-2014-7169 has been assigned to cover the vulnerability that is still present after the incorrect fix.
https://nvd.nist.gov/vuln/detail/CVE-2014-6271
7. CVE-2023-38039
When curl retrieves an HTTP response, it stores the incoming headers so that
they can be accessed later via the libcurl headers API.
However, curl did not have a limit in how many or how large headers it would
accept in a response, allowing a malicious server to stream an endless series
of headers and eventually cause curl to run out of heap memory.
https://nvd.nist.gov/vuln/detail/CVE-2023-38039
8. CVE-2023-27532
Vulnerability in Veeam Backup & Replication component allows encrypted credentials stored in the configuration database to be obtained. This may lead to gaining access to the backup infrastructure hosts.
https://nvd.nist.gov/vuln/detail/CVE-2023-27532
9. CVE-2023-3180
A flaw was found in the QEMU virtual crypto device while handling data encryption/decryption requests in virtio_crypto_handle_sym_req. There is no check for the value of `src_len` and `dst_len` in virtio_crypto_sym_op_helper, potentially leading to a heap buffer overflow when the two values differ.
https://nvd.nist.gov/vuln/detail/CVE-2023-3180
10. CVE-2022-44729
Server-Side Request Forgery (SSRF) vulnerability in Apache Software Foundation Apache XML Graphics Batik.This issue affects Apache XML Graphics Batik: 1.16.
On version 1.16, a malicious SVG could trigger loading external resources by default, causing resource consumption or in some cases even information disclosure. Users are recommended to upgrade to version 1.17 or later.
https://nvd.nist.gov/vuln/detail/CVE-2022-44729
Held annually on 28 January every year since 2007, Data Privacy Day was introduced by the Council of Europe to commemorate Convention 108 – the first, legally binding, international treaty on data protection signed in 1981. Data Privacy Day exists now to bring the concept of data privacy to the forefront, and encourage everyone to consider the steps they take to keep their data safe, and what more they could be doing.
The landscape of data privacy has changed dramatically since that first celebration in 2007. Wholesale changes to legislation have been implemented, new international regulations brought in and enforced, and on the whole, a shift in the dynamic of how the general public thinks about the privacy of their data.
Managing your data privacy can be a daunting task – our data is everywhere, and we’re not always consciously aware of what is happening to it. Unsecured data, oversharing online, interacting with suspicious communications – these are all things that the threat actors of the world rely on from their victims to achieve their criminal goals. Here are several simple things that can be done to improve your online privacy:
Social media is a gold mine of information for those with malicious intentions. Sharing events such as birthdays, names of loved ones, employment details etc, can allow a threat actor to very quickly socially engineer scams to encourage you to divulge sensitive information. Although we shouldn’t, quite often those details such as birthdays and loved ones’ names end up in our passwords too, so it doesn’t take much for a threat actor with a little motivation to work these out. Ensuring privacy settings are set to maximum, and not over-sharing, will do much to protect from these threats.
We receive a deluge of emails every day, in both our personal and work lives. Threat actors know this too which is why they’ll use email as a method to target individuals and businesses to gain access to sensitive data. Phishing scams rely on the innocent victim not realising that the email in front of them is fake, or trying to get them to do something they shouldn’t be doing. So if in doubt, stop and think before clicking on links or opening attachments.
Know your data privacy rights, and what applies in your country. In Europe, this will be GDPR, which gives a lot of control back to the person to whom the data relates. This includes:
Despite best efforts, threat actors are constantly looking for new and novel ways to gain access to our data, and inevitably, some of this will be stolen and used for criminal activity. SOS Intelligence has been diligently monitoring the digital landscape over 2023. Our recent findings are a stark reminder of the rising threat of phishing attacks. Over the past year, we have observed over half a million unique credentials compromised through phishing, and with the growth of Generative AI techniques, we expect that number to grow in 2024.
One standout feature of our technology is our real-time alert system. This capability ensures that our clients are promptly notified when their staff have fallen victim to phishing, allowing for a swift response and effective risk mitigation, helping you to ensure that your data remains as private as possible.
Photo by Jason Dent on Unsplash
2023 was a record year for cybercrime and threat actor activity, and we anticipate 2024 to be a continuation of this upward trend. Below we discuss a few key items we consider will be at the forefront of 2024’s cybersecurity landscape.
Expansion of ransomware operations
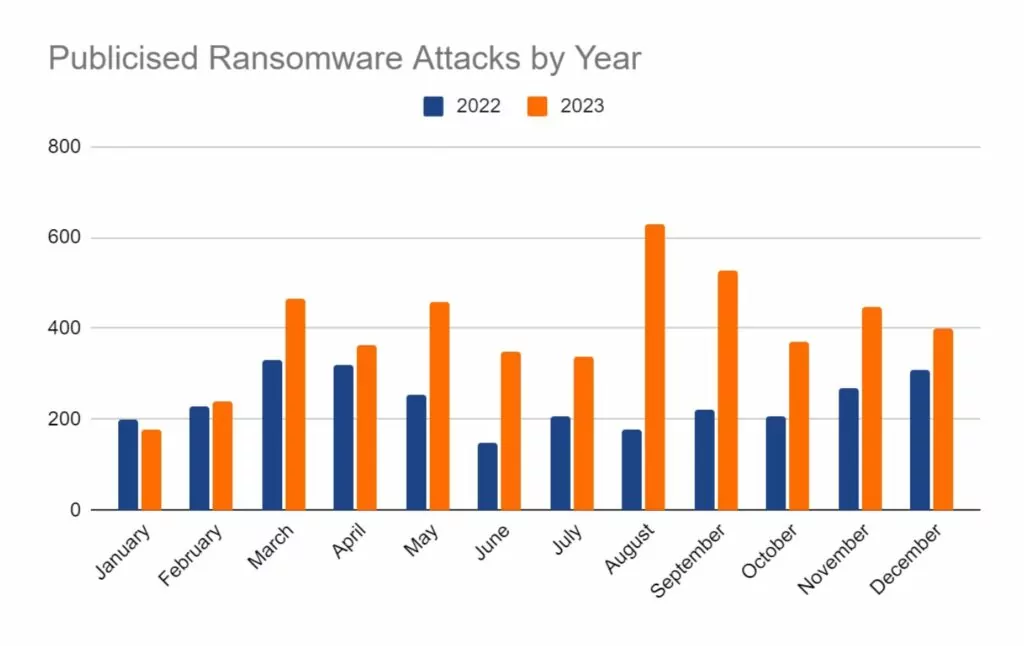
2023 was a record year for ransomware operators. Reported attacks were nearly double the numbers seen in 2022. The most successful groups operated as-a-service (RaaS), allowing them time to improve and develop their product whilst others worked to deploy the malware and bring in the money.
Law enforcement has been extremely active against these groups, taking down infrastructure relating to HIVE and ALPHV variants. However, in the latter’s case, this has seemingly slowed, but not halted their operations and they remain active in some capacity into 2024. Current data has shown a slight decline in the number of posts to their leak site however, this is a common pattern seen across many different variants and is likely due to the links to Russia and periods of inactivity over the holiday period.

We expect this year to be no exception to the continued growth of ransomware operations. It remains a lucrative opportunity for threat actors and the RaaS operating model allows less-skilled operators to partake in this criminal activity.
It is anticipated that ransomware tactics will expand to provide further opportunities to “motivate” victims into paying a ransom for their data. This will include the threat of deployment of “Wiper” malware – designed to fully delete an infected device or network in the event of non-compliance.
An increase in Supply Chain Attacks
It is highly anticipated that supply chain compromise will continue to be a tactic of choice for financially motivated and nation-state threat actors, who routinely and opportunistically scan the internet to identify unpatched systems ripe for exploitation.
The efficiency of supply chain attacks will likely be improved by both the infection and dissemination of software packages granting third-party access. This in turn allows threat actors to select and target their victims on a larger scale, leading to increased levels of compromise and wider attack surfaces for the deployment of malicious code. Subsequently, this will allow threat actors to better maintain persistence within victim networks, granting more time to conduct reconnaissance, analyse connected networks, and spread to encompass more victims.
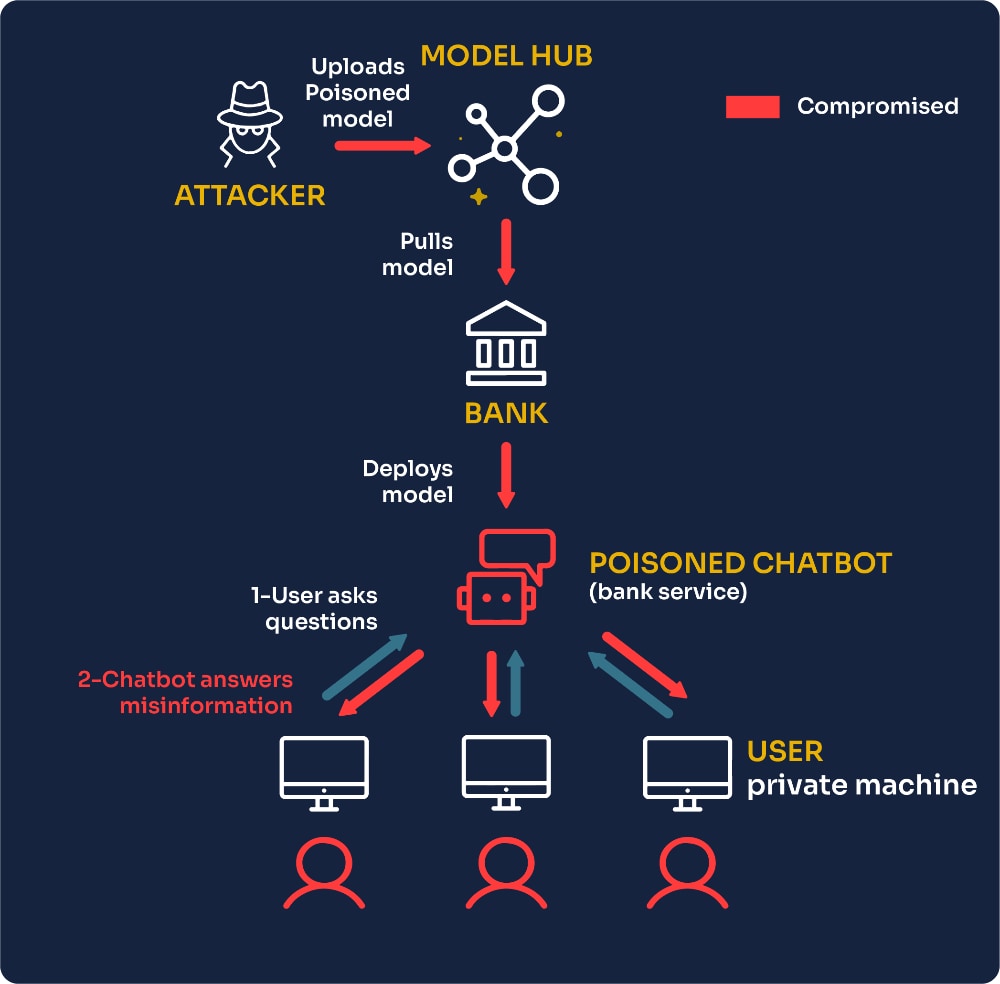
It is anticipated that supply chain attacks will target vulnerabilities in generative AI ecosystems. With AI and LLMs being utilised more and more to improve productivity, inevitably supply chains are becoming more interconnected. Failure to properly secure these components within the supply chain could be fatal, allowing threat actors to poison AI training data, manipulate updates, inject malicious algorithms, engage in prompt engineering, or exploit vulnerabilities as an entry point to compromise organisations’ data or systems.
The growth of AI-driven cyber-crime
AI has seen a massive boom in 2023, and this is expected to continue into 2024 and beyond as it becomes increasingly integrated into all manner of processes and procedures.
In 2024, we anticipate a surge in threat actors embracing AI to improve the quality and speed of development of the tools in their arsenal. This will include a quick and cost-effective way to develop new malware and ransomware variants. We also expect to see the increasing use of deepfake technologies to improve the standard of phishing and impersonation to support cyber-enabled frauds and business email compromise (BEC)
In contrast, it is anticipated that cyber security will employ a proactive strategy; as threat actors continue to harness the potential of AI and machine learning, cyber defenders will look to utilise similar techniques to counter these offensive tactics. The cyber security industry is already making substantial investments into the use of AI for defensive purposes, and this is expected to grow and be adopted by more in the field. Generative AI (GenAI)-powered capabilities such as automated code generation, reverse engineering, and document exploitation will reach previously unthinkable levels of sophistication and speed.
It is believed that GenAI will provide an improved toolkit to those targeting the human element when seeking to compromise network security. GenAI will provide threat actors with an easier method for developing more convincing phishing messages at scale, create video and audio deepfakes, and more easily collect information on their targets. This highlights the need in 2024 for an increased focus on awareness training to better prepare staff and colleagues for the inevitable surge of phishing attacks in 2024.
Key Global Events
Geopolitics is a key motivator for threat actors in certain sectors, particularly nation-states and hacktivists. Many key global events are scheduled for this year, providing high-profile targets for those who would seek to manipulate these events for their own gains.
Elections are due to be held in the following countries:

The BRICS group is due to expand, taking on the following new members: Egypt, Ethiopia, Iran, Saudi Arabia, and the United Arab Emirates. BRICS is now seen as an economic group to rival the G7, so it is anticipated that this expansion will lead to increased targeting of G7 financial institutions.
In July, the 2024 Summer Olympic Games will be held in Paris, France. Such events provide numerous opportunities for threat actors to make financial gains through fraudulent ticketing, and phishing to obtain financial data and credentials. Furthermore, it provides a canvas with global attention for those with a hacktivist agenda, ensuring their message reaches a wide audience.
Regulatory Changes Driving Threat Actor Innovation
Changes to regulations regarding the reporting of significant breaches, implemented in the USA by the Securities Exchange Commission (SEC), will force threat actors to hone and improve their stealth methods. We anticipate seeing increased focus on encryption and evasion techniques to allow threat actors to maintain undetected persistence within victim networks, to avoid triggering reporting to the SEC, and the expected forensic-level scrutiny that would follow. We believe that threat actors may look to non-material systems as a lower-risk target and entry point, quietly building their access, persistence and privileges from there before targeting higher-value network resources.
Additionally, we are also beginning to see ransomware groups using this new reporting requirement as an additional blackmail tool, threatening to report victims to the SEC themselves if their demands are not met. It is expected that this tactic will expand in use over the year to come.
What’s in store for SOS Intelligence in 2024
2024 looks to be an exciting year for SOS Intelligence.
Our team is growing further with a full time developer joining in early 2024. This will allow us to focus on improving the usability of the product, implement new features, and generate new data collection streams.
One of our key focus areas will be to improve the quality of the context around the data we provide. Improvements made to the platform will allow customers to see pertinent information relating to data sources, giving context to the risk and threat posed by that source. This will allow customers to make more informed decisions about the risks to their business or that of their clients.
We will also be looking to expand and improve the quality of our data collection. One particular focus will be on improving the reporting of CVEs. We aim to expedite alerts of new, high-risk vulnerabilities to our clients and subscribers so they can better mitigate and protect against the risks they pose.
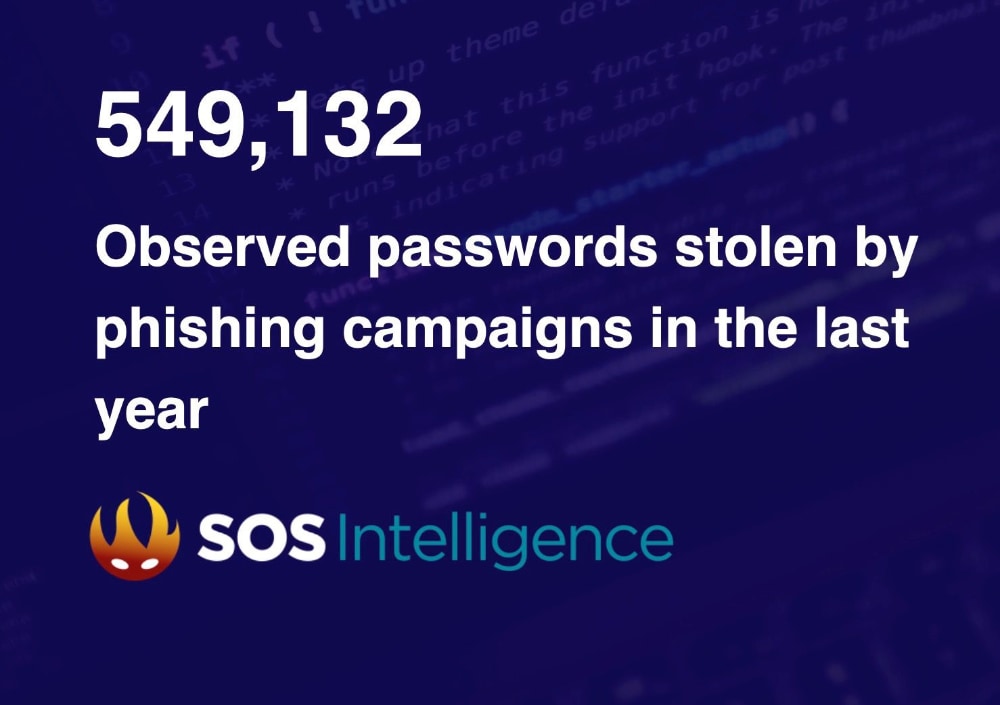
SOS Intelligence has been diligently monitoring the digital landscape over 2023. Our recent findings are a stark reminder of the rising threat of phishing attacks. Over the past year, we have observed over half a million unique credentials compromised through phishing, and with the growth of GenAI techniques, we expect that number to grow in 2024.
One standout feature of our technology is our real-time alert system. This capability ensures that our clients are promptly notified when their staff have fallen victim to phishing, allowing for a swift response and effective risk mitigation.
The unique services we provide at SOS Intelligence aren’t just about securing your digital assets; it’s a practical investment in proactive cybersecurity. Join us in creating a more secure digital environment.
Header Photo by freestocks on Unsplash
This weekly blog post is from via our unique intelligence collection pipelines. We are your eyes and ears online, including the Dark Web.
There are thousands of vulnerability discussions each week. SOS Intelligence gathers a list of the most discussed Common Vulnerabilities and Exposures (CVE) online for the previous week.
We make every effort to ensure the accuracy of the data presented. As this is an automated process some errors may creep in.
If you are feeling generous please do make us aware of anything you spot, feel free to follow us on Twitter @sosintel and DM us. Thank you!
1. CVE-2023-32560
An attacker can send a specially crafted message to the Wavelink Avalanche Manager, which could result in service disruption or arbitrary code execution.
Thanks to a Researcher at Tenable for finding and reporting.
Fixed in version 6.4.1.
https://nvd.nist.gov/vuln/detail/CVE-2023-32560
2. CVE-2023-34056
vCenter Server contains a partial information disclosure vulnerability. A malicious actor with non-administrative privileges to vCenter Server may leverage this issue to access unauthorized data.
https://nvd.nist.gov/vuln/detail/CVE-2023-34056
3. CVE-2023-34048
vCenter Server contains a partial information disclosure vulnerability. A malicious actor with non-administrative privileges to vCenter Server may leverage this issue to access unauthorized data.
https://nvd.nist.gov/vuln/detail/CVE-2023-34048
4. CVE-2023-29689
PyroCMS 3.9 contains a remote code execution (RCE) vulnerability that can be exploited through a server-side template injection (SSTI) flaw. This vulnerability allows a malicious attacker to send customized commands to the server and execute arbitrary code on the affected system.
https://nvd.nist.gov/vuln/detail/CVE-2023-29689
5. CVE-2019-14899
A vulnerability was discovered in Linux, FreeBSD, OpenBSD, MacOS, iOS, and Android that allows a malicious access point, or an adjacent user, to determine if a connected user is using a VPN, make positive inferences about the websites they are visiting, and determine the correct sequence and acknowledgement numbers in use, allowing the bad actor to inject data into the TCP stream. This provides everything that is needed for an attacker to hijack active connections inside the VPN tunnel.
https://nvd.nist.gov/vuln/detail/CVE-2019-14899
6. CVE-2023-1389
TP-Link Archer AX21 (AX1800) firmware versions before 1.1.4 Build 20230219 contained a command injection vulnerability in the country form of the /cgi-bin/luci;stok=/locale endpoint on the web management interface. Specifically, the country parameter of the write operation was not sanitized before being used in a call to popen(), allowing an unauthenticated attacker to inject commands, which would be run as root, with a simple POST request.
https://nvd.nist.gov/vuln/detail/CVE-2023-1389
7. CVE-2023-37569
This vulnerability exists in ESDS Emagic Data Center Management Suit due to lack of input sanitization in its Ping component. A remote authenticated attacker could exploit this by injecting OS commands on the targeted system.
Successful exploitation of this vulnerability could allow the attacker to execute arbitrary code on targeted system.
https://nvd.nist.gov/vuln/detail/CVE-2023-37569
8.
https://nvd.nist.gov/vuln/detail/
9.
https://nvd.nist.gov/vuln/detail/
10.
https://nvd.nist.gov/vuln/detail/
In the past week, the following vulnerabilities have been disclosed, affecting:
Ivanti ICS & Ivanti Policy Secure
CVSS: 8.2 HIGH
CVSS: 9.1 CRITICAL
Ivanti has disclosed the existence of two significant vulnerabilities affecting their Connect Secure and Policy Secure gateways, specifically versions 9.x and 22.x.
CVE-2023-46805 is an authentication bypass vulnerability, which allows a threat actor to remotely access restricted resources by bypassing control checks. CVE-2024-21887 is a command injection vulnerability, granting an authenticated user the ability to send specially crafted requests and execute arbitrary commands on the vulnerable device.
When utilised together, a threat actor can compromise a vulnerable device and execute code with admin rights, leaving the victim company open to a significant risk of network intrusion and further criminal activity.
Palo Alto’s Unit 42 has observed over 30,000 vulnerable devices spread across 141 countries. It is actively responding to incidents involving these vulnerabilities, highlighting their use by threat actors in the wild.
Ivanti is currently working on patches to fix these vulnerabilities. In the meantime, it is recommended that the mitigations they have suggested are implemented to avoid unnecessary risk. These can be found here.
Citrix NetScaler ADC & Citrix NetScaler Gateway
CVSS: 5.5 MEDIUM
CVSS: 8.2 HIGH
Citrix has identified and disclosed further vulnerabilities in its NetScaler ADC and NetScaler Gateway products. The following supported versions are affected:
*NetScaler ADC and NetScaler Gateway version 12.1 is now End Of Life (EOL) and is vulnerable
CVE-2023-6548 allows a threat actor authenticated, low-privileged access to remotely execute code on the management interface of a compromised device. This requires them to have access to the NSIP, CLIP or SNIP which itself has management interface access.
CVE-2023-6549 applies to appliances configured as one of the following:
Exploitation of this vulnerability involves a threat actor restricting operations within the memory buffer, thereby causing an unauthenticated Denial of Service attack.
A patch will follow in due course, but in the meantime, Citrix recommends the following:
Citrix has noted that these vulnerabilities have been observed in the wild and targeted by threat actors.
This weekly blog post is from via our unique intelligence collection pipelines. We are your eyes and ears online, including the Dark Web.
There are thousands of vulnerability discussions each week. SOS Intelligence gathers a list of the most discussed Common Vulnerabilities and Exposures (CVE) online for the previous week.
We make every effort to ensure the accuracy of the data presented. As this is an automated process some errors may creep in.
If you are feeling generous please do make us aware of anything you spot, feel free to follow us on Twitter @sosintel and DM us. Thank you!
1. CVE-2023-51467
Pre-auth RCE in Apache Ofbiz 18.12.09.
It’s due to XML-RPC no longer maintained still present.
This issue affects Apache OFBiz: before 18.12.10.
Users are recommended to upgrade to version 18.12.10
https://nvd.nist.gov/vuln/detail/CVE-2023-51467
2. CVE-2023-49070
Pre-auth RCE in Apache Ofbiz 18.12.09.
It’s due to XML-RPC no longer maintained still present.
This issue affects Apache OFBiz: before 18.12.10.
Users are recommended to upgrade to version 18.12.10
https://nvd.nist.gov/vuln/detail/CVE-2023-49070
3. CVE-2016-10509
SQL injection vulnerability in OpenCart v.2.2.00 thru 3.0.3.2 allows a remote attacker to execute arbitrary code via the Fba plugin function in upload/admin/index.php.
https://nvd.nist.gov/vuln/detail/CVE-2016-10509
4. CVE-2018-13067
SQL injection vulnerability in OpenCart v.2.2.00 thru 3.0.3.2 allows a remote attacker to execute arbitrary code via the Fba plugin function in upload/admin/index.php.
https://nvd.nist.gov/vuln/detail/CVE-2018-13067
5. CVE-2018-11494
SQL injection vulnerability in OpenCart v.2.2.00 thru 3.0.3.2 allows a remote attacker to execute arbitrary code via the Fba plugin function in upload/admin/index.php.
https://nvd.nist.gov/vuln/detail/CVE-2018-11494
6. CVE-2023-4966
Sensitive information disclosure in NetScaler ADC and NetScaler Gateway when configured as a Gateway (VPN virtual server, ICA Proxy, CVPN, RDP Proxy) or AAA virtual server.
https://nvd.nist.gov/vuln/detail/CVE-2023-4966
7. CVE-2020-20491
SQL injection vulnerability in OpenCart v.2.2.00 thru 3.0.3.2 allows a remote attacker to execute arbitrary code via the Fba plugin function in upload/admin/index.php.
https://nvd.nist.gov/vuln/detail/CVE-2020-20491
8. CVE-2023-47444
SQL injection vulnerability in OpenCart v.2.2.00 thru 3.0.3.2 allows a remote attacker to execute arbitrary code via the Fba plugin function in upload/admin/index.php.
https://nvd.nist.gov/vuln/detail/CVE-2023-47444
9. CVE-2023-5360
An issue has been discovered in GitLab CE/EE affecting all versions from 16.1 prior to 16.1.6, 16.2 prior to 16.2.9, 16.3 prior to 16.3.7, 16.4 prior to 16.4.5, 16.5 prior to 16.5.6, 16.6 prior to 16.6.4, and 16.7 prior to 16.7.2 in which user account password reset emails could be delivered to an unverified email address.
https://nvd.nist.gov/vuln/detail/CVE-2023-5360
10. CVE-2023-46747
An issue has been discovered in GitLab CE/EE affecting all versions from 16.1 prior to 16.1.6, 16.2 prior to 16.2.9, 16.3 prior to 16.3.7, 16.4 prior to 16.4.5, 16.5 prior to 16.5.6, 16.6 prior to 16.6.4, and 16.7 prior to 16.7.2 in which user account password reset emails could be delivered to an unverified email address.
https://nvd.nist.gov/vuln/detail/CVE-2023-46747
SOS Intelligence is currently tracking 170 distinct ransomware groups, with data collection covering 319 relays and mirrors.
In the reporting period, SOS Intelligence has identified 373 instances of publicised ransomware attacks. These have been identified through the publication of victim details and data on ransomware blog sites accessible via Tor. Our analysis is presented below:
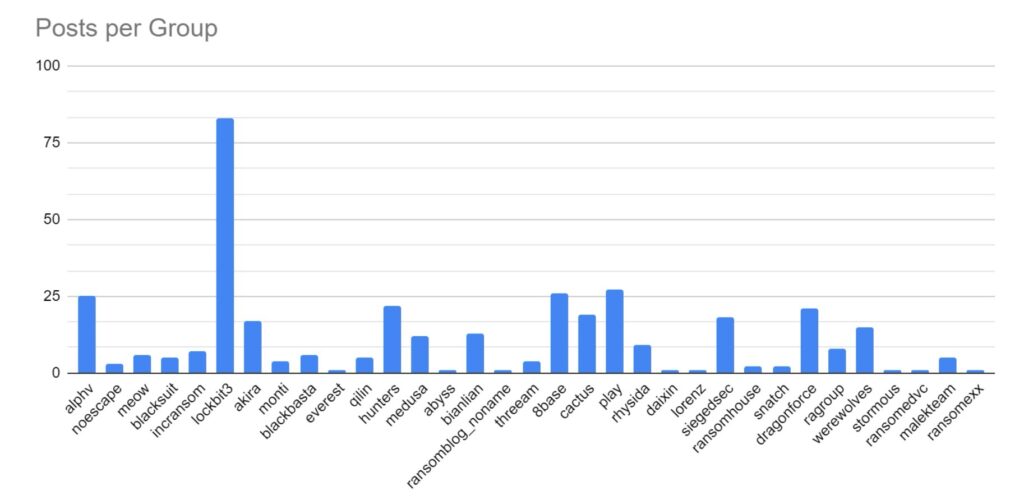
We first look at strain activity. As ever, the ransomware landscape is dominated by strains using affiliate models (Ransomware-as-a-Service (RaaS)). Lockbit remains the most active strain, and while there has been a decrease in overall activity, it maintains a 22% market share. 8base, AlphV and Play remain significantly active, but this month we have also seen significant activity by Hunters (RaaS), Cactus (RaaS), and Dragonforce.
Dragonforce are a newly emerged group, with little known about them at the time of print. Given the level of successful disruption by law enforcement during 2023, it is suspected that this group may be a rebranding of a previous threat group.
The Werewolves group has been observed increasing their level of attacks. The group appears relatively new, however, they have taken responsibility for a 2022 attack on the Electric Company of Ghana which resulted in significant power outages. The veracity of this claim is not known. Their level of activity is called into question by several of their victims also appearing on the LockBit breach site. Six identical posts were seen across both sites. Additionally, the ransomware used is a public domain version of Lockbit3, while their attacks make use of tools leaked from the Conti group. This would seem to indicate that the group was previously an affiliate of LockBit.
What makes this group standout is the targeting of Russian victims. Ransomware groups and operators are quite often pro-russian, with several groups supporting the Russian government publicly in its war against Ukraine. The targeting may explain a potential split from LockBit, and hint at a possible location for the group.
Finally, we have observed increased activity from the SiegedSec group. They appear focused more on data exfiltration, and are politically, rather than financially, motivated. Their focus has been on hacktivism, with a significant focus on targeting Israel and the USA.
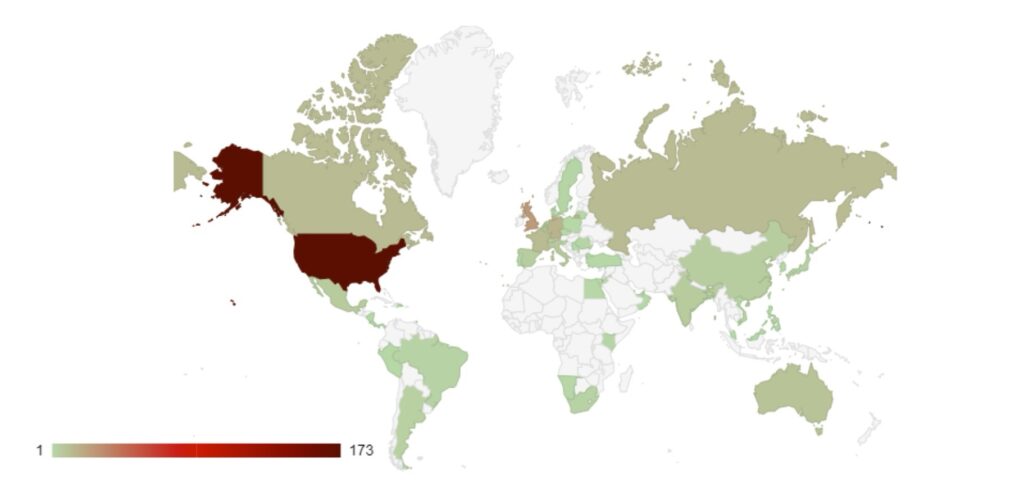
As seen in previous months, the USA remains the primary target of ransomware groups and threat actors. We have observed a steady release of data from Canada, France, Germany, Italy, and the UK. As members of the G7, these countries have strong economies and therefore possess lucrative targets for financially-minded threat actors.
However, this surge in activity may be politically motivated. In recent weeks these countries have all shown support for Israel in its conflict with Hamas, which may give certain threat actors additional motivation to target those countries. As highlighted previously, there have also been significant increases in the targeting of Israel and Russia.
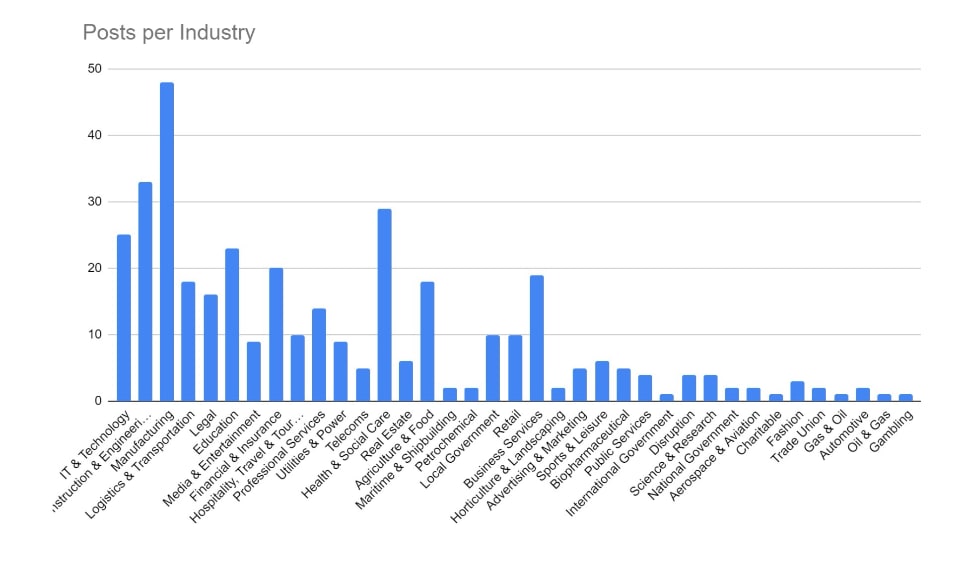
Manufacturing, Construction and Engineering, and IT and Technology have remained the key targeted industries for December. These industries would be more reliant on technology in order to continue their business activities, and so it logically follows that they would be more likely to pay a ransom in order to regain access to compromised computer systems. The Financial and Education sectors have also seen increased activity over the period.
We are seeing a shift in tactics for certain industries, particularly those where data privacy carries a higher importance (such as legal or healthcare), where threat actors are not deploying encryption software and instead relying solely on data exfiltration as the main source of material for blackmail and extortion.
| Cookie | Duration | Description |
|---|---|---|
| cookielawinfo-checkbox-analytics | 11 months | This cookie is set by GDPR Cookie Consent plugin. The cookie is used to store the user consent for the cookies in the category "Analytics". |
| cookielawinfo-checkbox-functional | 11 months | The cookie is set by GDPR cookie consent to record the user consent for the cookies in the category "Functional". |
| cookielawinfo-checkbox-necessary | 11 months | This cookie is set by GDPR Cookie Consent plugin. The cookies is used to store the user consent for the cookies in the category "Necessary". |
| cookielawinfo-checkbox-others | 11 months | This cookie is set by GDPR Cookie Consent plugin. The cookie is used to store the user consent for the cookies in the category "Other. |
| cookielawinfo-checkbox-performance | 11 months | This cookie is set by GDPR Cookie Consent plugin. The cookie is used to store the user consent for the cookies in the category "Performance". |
| viewed_cookie_policy | 11 months | The cookie is set by the GDPR Cookie Consent plugin and is used to store whether or not user has consented to the use of cookies. It does not store any personal data. |


Recent Comments